Protect Your Business with the IT Security Plan Procedure Template Word
Are you concerned about the security of your business’s IT systems? Do you want to ensure that your company’s sensitive information is protected from cyber threats? Look no further than the IT Security Plan Procedure Template Word from Bizmanualz.
This comprehensive template provides a step-by-step guide to creating an effective IT security plan for your business. It includes detailed procedures for identifying potential security risks, implementing security measures, and responding to security incidents.
With the IT Security Plan Procedure Template Word, you can rest assured that your business’s IT systems are secure and protected from cyber threats. The template is easy to use and can be customized to meet the specific needs of your business.
In addition to providing a comprehensive IT security plan, the template also includes procedures for training employees on IT security best practices and conducting regular security audits to ensure ongoing compliance.
Don’t leave the security of your business’s IT systems to chance. Invest in the IT Security Plan Procedure Template Word from Bizmanualz and protect your company’s sensitive information from cyber threats. Order now and get started on creating a secure and resilient IT infrastructure for your business.
IT Security Plan Procedure
Maintain your IT security policies with our IT Security Plan Procedure. The IT Security Plan Procedure provides an overview of the your company’s IT network’s security requirements and describes what controls should be in place to meet the requirements. The IT Security Plan Procedure also ensures all personnel who access your company’s system understand their security responsibilities.
This IT Security Plan Procedure applies to all of your company’s IT assets and to all personnel (26 pages, 5868 words) and is part of the IT Policies and Procedures Manual.
IT Security Plan Job Responsibilities:
The Information Technology Security Manager is responsible for preparing and developing the Information Technology Security Plan and implementation schedule, implementing the Plan and any updates, and monitoring and periodic reporting on the Plan.
Information Technology Managers are responsible for establishing and periodically convening the Security Review Committee, advising the Information Technology Security Manager regarding development of the Plan, coordinating with Human Resources Management to provide user training, and verifying implementation of updates to the Plan.
The Security Review Committee is responsible for periodic review and updates and for final approval of the Information Technology Security Plan.
IT Security Plan Definition:
Security – The state of being free from danger or injury. The effort to create a secure computing platform, designed so that agents (users or programs) can only perform actions that have been allowed.
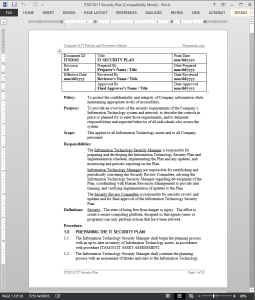 IT Security Plan Procedure Activities
IT Security Plan Procedure Activities
- Preparing the IT Security Plan
- Developing the IT Security Plan
- Implementing the IT Security Plan
- IT Security Plan Review
- IT Security Plan Update
IT Security Plan Procedure References
- ISO/IEC 27001:2013 Information Technology-Code of Practice for Information Security Management
- National Institute of Standards and Technology (NIST) Special Publication #800-18- Guide for Developing Security Plans for Information Technology Systems (December, 1998)
- National Institute of Standards and Technology (NIST) Special Publication #800-43- Systems Administration Guidance for Windows 2000 Professional (November, 2002)
IT Security Plan Procedure Forms
- IT Security Assessment Checklist Form
- IT Security Plan Form
- IT Security Plan Implementation Schedule
Computers and IT have become important parts of business operations, storing and circulating critical information between numerous business processes. Many business functions require the use of computer systems and networks, and businesses and computer networks are increasingly interconnected.
But how do you govern these systems and what standards do you choose? In other words, how much should you think about coordinating and securing the information that is so important to you and your business?
Information Security
Any information is susceptible to leakage or damage unless protected by a strong security system. Information stored in computers is no exception. With the high usage of computers, servers and many systems connected by layers of networks, security is one of the key challenges for IT professionals today. We hear so much about identity theft, virus infections or spyware hijacks. At various levels, all these activities put heavy burdens on your resources.
In order to preempt this threat and protect your information, you must have information security measures in place to maximize results. This means developing and implementing a set of controls through appropriate policies, procedures and processes. Besides meeting your organization’s goals and objectives, these controls should also be aligned with other business processes in your organization.
IT Governance
This is where the issue of IT governance comes in. The executive summary of COBIT or the Control Objectives for Information and Related Technology identifies IT governance as “a structure of relationships and processes to direct and control the enterprise in order to achieve the enterprise’s goals by adding value while balancing risk versus the return or IT and its processes.” In other words, IT governance is about balancing risk and return from your IT processes.
So how do you approach IT governance? Businesses can either create their own structures and frameworks, or adopt universally accepted “best practices” standards that have been tried, tested and improved by a large number of organizations and individuals. Implementing an IT quality standard has its own benefits.
IT Standards
Two main IT standards available today are COBIT and ISO 27000.
Currently in its third edition, COBIT is a framework for managing IT risk and was created by the Information Systems Audit and Control Association (ISACA), and the IT Governance Institute (ITGI). It consists of 34 high level objectives covering 318 control objectives categorized in four areas—planning and organization, acquisition and implementation, delivery and support and monitoring.
The six elements of COBIT are documented in separate volumes and include management guidelines, control objectives, COBIT framework, executive summary, audit guidelines and an implementation toolset.
ISO17799 was originally published in 2000 by the International Organization for Standardization, which reissued a revised version in 2005 and changed the name to ISO 27001 and was updated again 2013. It is based on the British Standard BS7799 from 1995 and focuses on security with an aim to help organizations create effective security plans.
The ten main sections of ISO 27001 are: security policy, security organization, asset classification and control, personnel security, physical and environmental security, communications and operations management, access control, systems development and maintenance, business continuity management, and compliance.
Benefits of IT Standards
Adopting an IT Standard, by itself, may not mean that your organization is 100% secure. However, compliance with these established standards goes a long way in demonstrating that you take security issues very seriously. On the top level, four obvious benefits of IT standards stand out:
COMPLETENESS
Like any other internationally accepted standard, IT standards spare you from reinventing the wheel. Why spend the time and resource creating something that already exists and is proven to work?
COMPLIANCE
Using a widely regarded standard demonstrates that the organization practices industry norms and follows applicable laws and regulations.
CREDIBILITY
Having a standard in place reassures stakeholders of the company, including customers, suppliers, and employees by demonstrating that your organization is committed towards protecting valuable information.
CONFIDENCE
By minimizing risk of information leakage, IT standards lead to better knowledge management and more efficient use of your IT assets.
















Reviews
There are no reviews yet.