Streamline Your Use of Non-Standard Software with Our Procedure Template for Word
Are you tired of dealing with the headaches that come with using non-standard software in your organization? Our Use of Non-Standard Software Procedure Template for Word can help you streamline the process and ensure that everyone is on the same page.
With this template, you’ll have a clear and concise set of guidelines for using non-standard software, including how to request approval, how to install and configure the software, and how to ensure that it’s being used in a secure and compliant manner.
Our Use of Non-Standard Software Procedure Template for Word is fully customizable, so you can tailor it to your organization’s specific needs and requirements. Whether you’re a small business or a large enterprise, this template can help you save time and reduce the risk of errors and security breaches.
Some of the key features of our Use of Non-Standard Software Procedure Template for Word include:
- Clear and concise guidelines for requesting, installing, and using non-standard software
- Step-by-step instructions for ensuring that the software is being used in a secure and compliant manner
- Customizable sections for adding your own policies and procedures
- Easy-to-use format that can be shared with employees and stakeholders
Don’t let the use of non-standard software cause unnecessary headaches and risks in your organization. Get our Use of Non-Standard Software Procedure Template for Word today and start streamlining your processes and improving your security and compliance.
Use of Non-Standard Software Procedure
The Use of Non-Standard Software Procedure delineates specific guidelines regarding the use of personal software on company computing assets. This procedure helps ensure the efficiency and supportability of company computing resources, strict software configuration control procedures are required. The use of personally owned, unlicensed, or unauthorized software on company computing assets is prohibited. It applies to all company personnel and company computer equipment and systems. (6 pages, 789 words)
In some cases, the need for a software solution outside the scope of the Common Operating Environment (COE) will arise. When a system user identifies such a requirement, that user should submit a formal request for permission to install and use the non-standard software program. This request should be forwarded via the user’s department director to the Information Systems Manager.
Use of Non-Standard Software Responsibilities:
The Information Systems Manager is responsible for reviewing and approving requests to use non-standard software.
Department directors/managers are responsible for enforcing company policy and standards regarding software configuration and use.
Computer system users are responsible for knowing and observing company policy and standards regarding software configuration and use. Users must seek and receive approval before installing or using non-standard software on company computing assets. If unauthorized software is found or suspected, users are responsible for notifying their Department managers.
Company LAN Administrators are responsible for monitoring software installation, configuration, and usage. They are also responsible for reporting violations to the Information Systems Manager and Information Security Manager and, when unauthorized software is detected, coordinating actions required to eradicate the unauthorized software and return the workstation or system to the approved configuration.
The Information Security Manager is responsible for ensuring that software installed on company IT assets – authorized or not – does not pose a security threat and ensuring that users have appropriate access to company software and information.
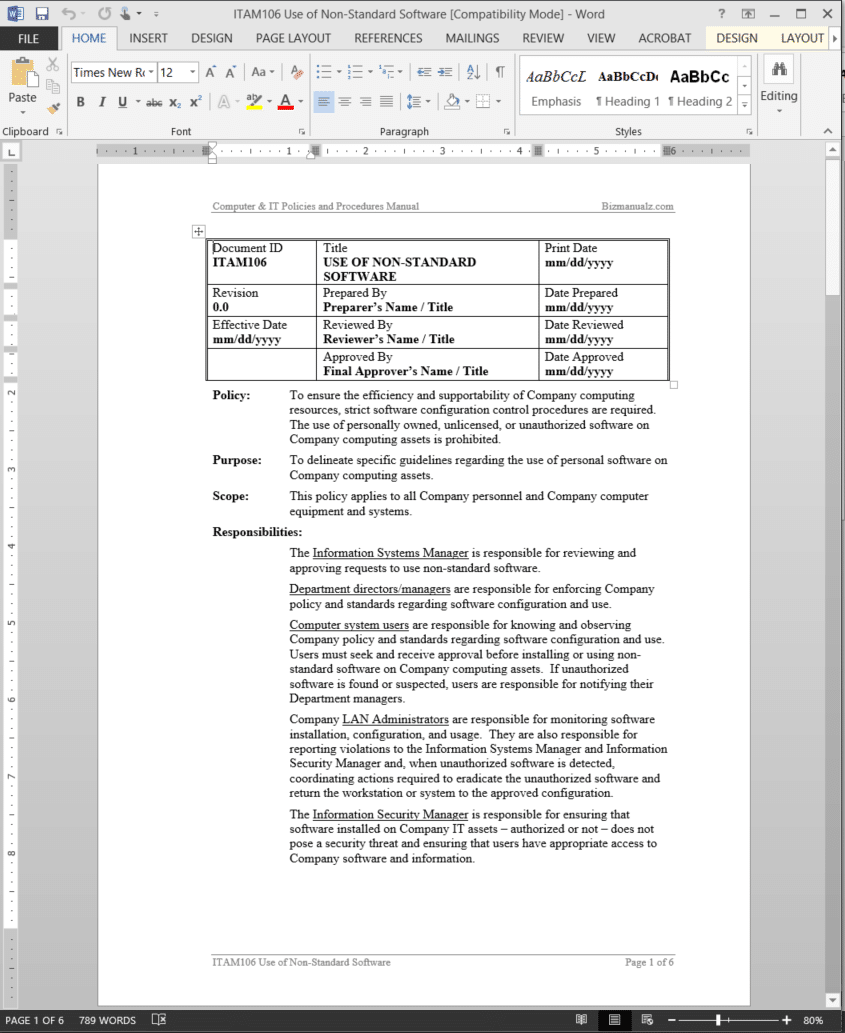 Use of Non-Standard Software Procedure Activities
Use of Non-Standard Software Procedure Activities
- Requesting Non-Standard Software
- Adding Non-Standard Software to the COE
- Software Not Permitted Under Any Circumstances
Use of Non-Standard Software Procedure Forms

















Reviews
There are no reviews yet.