Keep Track of Incidents with the Acceptable Use Incident Log Template Word
As a business owner, it’s important to ensure that your employees are using company resources appropriately. The Acceptable Use Incident Log Template Word is a tool that can help you keep track of any incidents that occur related to the use of company resources.
This template is easy to use and can be customized to fit the needs of your business. It includes fields for recording the date and time of the incident, the employee involved, a description of the incident, and any actions taken in response.
By using this template, you can quickly and easily document any incidents that occur, which can be helpful in identifying patterns or trends. It can also be used as a tool for training employees on appropriate use of company resources.
The Acceptable Use Incident Log Template Word is available for download from Bizmanualz. It is compatible with Microsoft Word and can be easily customized to fit the needs of your business. With this tool, you can ensure that your employees are using company resources appropriately and that any incidents are documented and addressed in a timely manner.
Don’t let incidents related to the use of company resources go undocumented. Download the Acceptable Use Incident Log Template Word today and start keeping track of any incidents that occur.
>Acceptable Use Incident Log Template
The Acceptable Use Incident Log Template provides an example register of incidents relating to Acceptable Use violations. DEV104-2 AUP INCIDENT LOG covers date, ID, description, category, and status. Company users who identify or perceive an actual or suspected security problem should immediately contact the company IT Manager for the incident to be logged in Human Resources Incident Log. Users should not reveal account password or allow another person to use their account. Similarly, users should not use the account of another user. Access to company network resources should be revoked for any user identified as a security risk or a demonstrated history of security problems.
Access to the Internet is specifically limited to activities in direct support of official company business or for educational and research purposes. If any user has a question regarding what constitutes “acceptable use” he/she should check with their supervisor for additional guidance. Management or supervisory personnel should consult with the Information Services Manager for clarification of these guidelines. The company Internet access should not be used for any illegal or unlawful purposes. Examples include the transmission of violent, threatening, defrauding, pornographic, obscene, or otherwise illegal or unlawful materials.
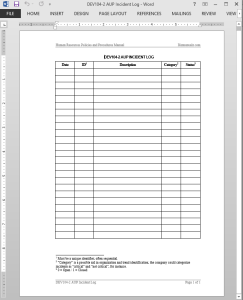 Acceptable Use Incident Log Template Details
Acceptable Use Incident Log Template Details
Pages: 01
Words: 40
Format: Microsoft Word 2013 (.docx)
Language: English
Manual: Human Resources
Category: Development
Procedure: Internet Email Acceptable Use Procedure DEV104
Type: Log


















Reviews
There are no reviews yet.