Save Time Writing Procedures
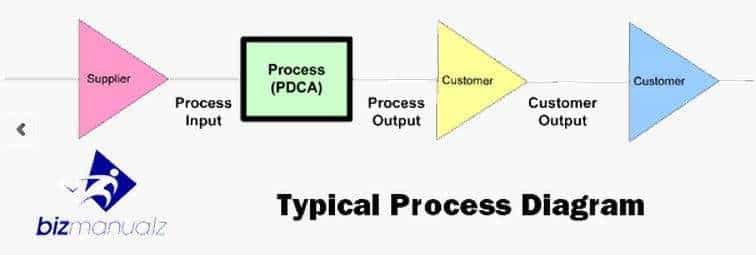
Project management follows a common Plan-Do-Check-Act (PDCA) cycle found within the five project phases. Do you know what these phases are?
Read moreAll policies and procedures manuals from Bizmanualz follow the Plan-Do-Check-Act (PDCA) cycle. The new procedure writing guide emphasizes this concept.
Read moreBest practices are must-follow guidelines for success. They help streamline processes, increase efficiency, minimize risks, and improve performance. Adhering to best practices creates consistency and makes it easier for teams to reach common goals. It also promotes knowledge transfer, allowing employees to learn from each other. This encourages continuous improvement and innovation. What is the meaning […]
Read moreDon’t just write about your tasks, learn how to Get results from your procedures.
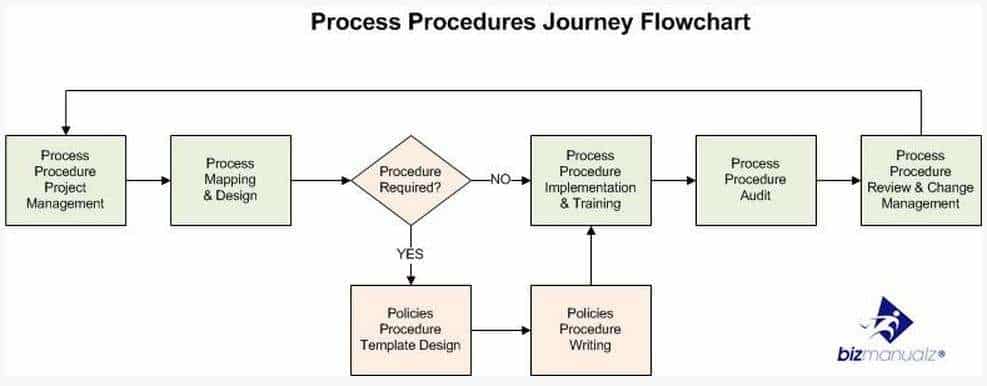
Read moreWhen many of us see change coming, we’re not sure what to do. We sometimes fear or mistrust change, or we put off big problems because they’re “too much all at once”, and we stick with outdated, inefficient tools, methods, and processes. How do You Develop Procedures Quickly?
Read moreUsing Bizmanualz procedures with minor modifications can save you as much as 38 hours of time.
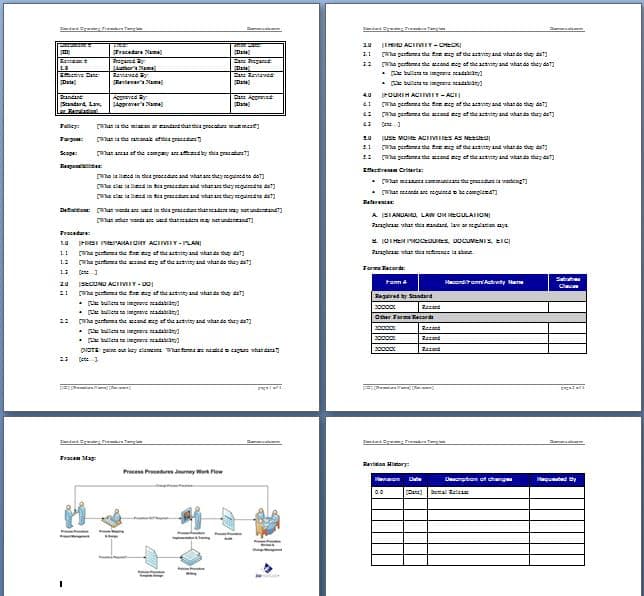
Read moreEver try making a blank template for your procedures using Microsoft Word?
Read moreToday’s business owners, CIOs, COOs, and business leaders are required to comply with a plethora of federal regulations and international standards. Bizmanualz is ready to help.
Read moreBusiness writing isn’t hard, but when it comes to professional communication, many of us feel intimidated by the lack of experience in the field or feel we don’t have “the talent” for writing. The truth is, to write a quality piece of business content, you don’t have to be a gifted writer. All you have […]
Read more